In the starting phase of my career, my clients reported to me a peculiar issue. They said that they get redirected to a session expired page even before they actually login.
In that application, we developed a generic methodology, then whenever a user clicks on any action that requires a postback, it first checks whether the session has expired or not and if expired, then redirects to a custom session expired page. Later, the user can click on the login link and is redirected to the login page.
I analyzed that issue and found that users used to open the website home page which is obviously the login page and some of them left the page for a while around 15 or more minutes and after that when they went back to the system, they used to enter the credentials and click on the login button, and it redirected them to a session expired page.
It left them annoyed and even me too. I have myself seen many applications where I open the login page and after sometime, when I enter my login details, it redirects me to a session expired page.
Some of my colleagues were saying, how can a session expire even before a successful login? I have also found many other developers having the same question. So I thought of writing a blog post on it.
First, let me explain how the session works:
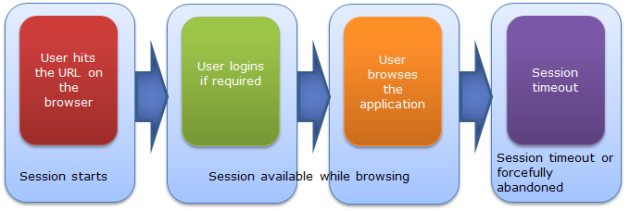
As you can see above, as soon as the user accesses the site and the first page gets opened, the countdown of the session timeout starts. So it does not matter whether you login or not, session will be expired after the specified amount of time. So if your website does not have a check on session expiration before login, it won't be visible to your user and even if the user logs in after the specified amount of time, a new session will be created.
But so many people get confused about authentication and session. Session start and expire does not have any connection with authentication start and authentication timeout. Authentication works separately.
As you know, when a user requests a page, it goes through many HTTPModules and is lastly served by an HTTPHandler. We can show it pictorially as:

As you can see, an ASP.NET request goes through many HTTPModules and is finally served by an HTTPHandler. Many features of ASP.NET are developed as HTTP modules. Session and authentication are also developed as HTTPModules . For session handling, we have SessionStateModule which is available under the namespace System.Web.SessionState and various authentication mechanisms in ASP.NET like Form Authentication are also available via an HTTPModule FormsAuthenticationModule which is under the namespace System.Web.Security. So, these two are separate modules and work independently.
Normally in our application, as soon as a user clicks on sign out, we used to kill session. Normally, we set authentication timeout and session timeout the same but what may happen if we have...
<forms timeout="15" loginUrl="Login.aspx" name=".ASPXFORMSAUTH">
...and:
<sessionState timeout="10">
What could happen?

As you can see in the above scenario, I have set the session time out to be less than authentication timeout. After browsing for 5 mins, I left it for around 12 mins and my session gets timed out. Because my session time out is 10 mins while my authentication time out is 15 mins. But I’ll still be authenticated and be able to browse my application even if my session expires and gets recreated and my existing session data is lost.
Normally, we put the authentication timeout and session timeout as the same. This is just the first step to avoid the discrepancy between the timeout of authentication and session.
But in certain browsers, it behaves differently. Like session gets timed out if the last request made was 10 (in my example session timeout is 10 minutes) or more minutes and on every request, the counter gets reset for 10 minutes, but authentication timeout does not work the same way in all browsers. Like if I have authentication timeout for 10 minutes, the authentication timeout counter does not get reset on every request to 10 minutes. Sometimes, there are some performance improvements that are done which resets on the counter only at certain points say if after 5 or 7 minutes, as to reset the authentication timeout on very request is costly. And this may lead to discrepancy.
Other scenarios, if somehow IIS gets reset, the sessions of users connected to that web server will become invalid while the user authentication will still be valid.
To avoid any unprecedented events like the above, I put a check for an authentication and session on every page, so that the user cannot proceed further if the session or authentication is not valid. Also, if we found the user is not authenticated any more, then we clear and abandon the session and redirect the user to the login page. Similarly, if the session is not available, then we remove the user and the authentication as well.
Also, at the time of user clicking on Logoff, we should clear and abandon the session so that the same session is not available after Logoff.
As you can see, session and authentication work separately and they work parallely and independently.
For the problem stated earlier in this post, I suggest a solution to avoid the issue but you can put your own logic to prevent the issue.
Hope you all have enjoyed this post. Please share your valuable feedback.
