- home
- articles
- quick answersQ&A
-
discussionsforums
- CodeProject.AI Server
- All Message Boards...
- Application Lifecycle>
- Design and Architecture
- Artificial Intelligence
- ASP.NET
- JavaScript
- Internet of Things
- C / C++ / MFC>
- C#
- Free Tools
- Objective-C and Swift
- Database
- Hardware & Devices>
- Hosting and Servers
- Java
- Linux Programming
- Python
- .NET (Core and Framework)
- Android
- iOS
- Mobile
- WPF
- Visual Basic
- Web Development
- Site Bugs / Suggestions
- Spam and Abuse Watch
- featuresfeatures
- communitylounge
- help?
Everything / Security
Security
security
Great Reads
by The Ænema
Inject your 4.
by Michael Haephrati
Chrome stores all passwords and other credentials in an encrypted database but guess what: they can be retrieved by anyone with the proper knowledge.
by Ajay K. Yadav
The objective of writing this paper is to manifest,
by Kewin Rausch
An introduction on how these applications self-defend themselves against scanning techniques,
Latest Articles
by Jason Sultana
This article discusses Cross Site Scripting (XSS),
by Wessel Beulink
What is Azure Virtual Network Encryption? Azure Virtual Network encryption provides a layer of security that encrypts virtual network traffic,
by Zijian
Reusable codes for JWT security in business applications
by Federico Di Marco
A tool which creates one or more Powershell scripts which in turn recreate one or more binary files
All Articles
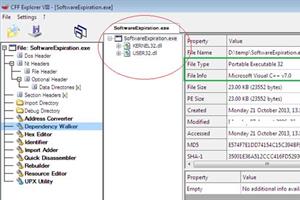
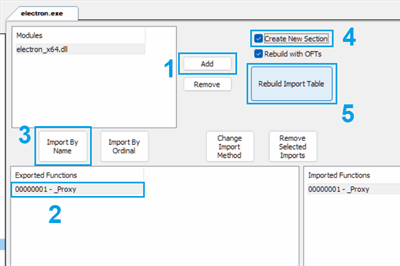
28 Oct 2014 by Ajay K. Yadav
The objective of writing this paper is to manifest, how to crack an executable without peeping its source code by exercising OllyDbg tool.
11 Jun 2014 by Steve Wellens
There was a question from a student over on the Asp.Net forums about improving site performance. The concern was that every time an app setting was read from the Web.Config file, the disk would be accessed. With many app settings and many users, it was believed performance would suffer.
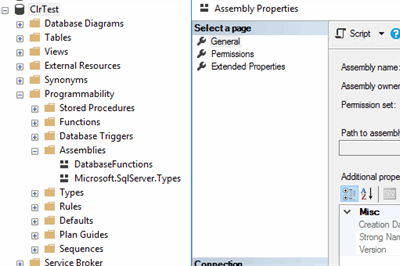
8 Feb 2022 by Pavel Bashkardin
30 Jan 2017 by Michael Haephrati
20 Jun 2013 by Levente Kupás
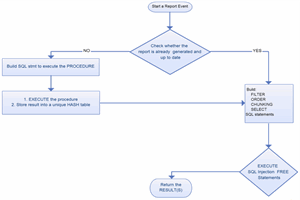
If you have big reports which run slowly, you may use this T-SQL based engine to speed-up them.
19 Feb 2022 by Asif Bahrainwala
10 Mar 2018 by Joe Dillon
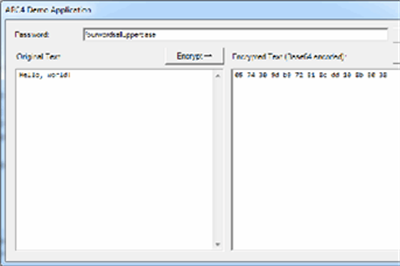
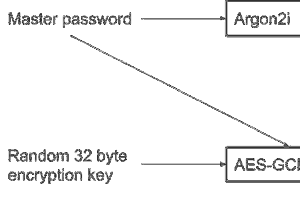
This article describes the security techniques required to create a secure offline password manager and how the Libsodium library has been used to achieve this. YAPM stores passwords with AES encryption and authenticates users with an Argon2 hash.
26 Jan 2010 by #realJSOP
19 Aug 2014 by Sergey Alexandrovich Kryukov
14 Jun 2011 by Tamir Khason
How to import OpenSSL private key into .NET application and use it with X509 public certificate to establish TLS connection with asymmetric encryption and two phase certificates handshake
22 Apr 2018 by Rajat-Indiandotnet
16 Jan 2023 by The Ænema
23 Apr 2010 by Pete O'Hanlon
Bear in mind that you expose methods via a contract. If you do not want people to have access to 5 of those methods, just expose a contract that has the remaining 5 methods and use that instead. You can have exactly the same code in place implementing the contracts, as long as the two...
21 Aug 2010 by Vinayaka Krishna Shenoy
17 Jun 2012 by Espen Harlinn
27 Jan 2014 by whoisrich
16 Sep 2015 by Sergey Alexandrovich Kryukov
One way to preserve some file from modifications or deletion, regardless of privileges, is to keep it permanently open in some process, for non-shared access (which is the default). To keep this state permanent, the code should also be executed permanently, which is possible if this process is...
15 Mar 2016 by Jochen Arndt
It is returning a length of 350 because the string contains 350 characters.To verify this, select the text and paste it into an Unicode editor (e.g. with Notepad++ choose File - New, Encoding - UCS-2 Little Endian, and paste the text). Within Notepad++, it will look like (shortened, there...
18 Jul 2016 by OriginalGriff
We do not condone, support, or assist in the production of malicious code in any way, form, or manner. This is a professional site for professional developers.And trying to remove any of the security features that the user has applied to his device is a malicious activity.If you want to...
10 Nov 2018 by DataBytzAI
18 Feb 2019 by Apriorit Inc, ruksovdev
A detailed description of an FPGA-specific framework called ISE Design Suite, and the main steps you need to take in order to create a VGA driver using FPGA
2 Mar 2023 by Lee P Richardson
6 Feb 2011 by Sergey Alexandrovich Kryukov
If you use Window 7, the solution is the BitLocker: http://technet.microsoft.com/en-us/library/ee449438(WS.10).aspx#BKMK_WhatIsBitLocker[^]. It will work with removable drives, of course.I'll understand if you cannot accept this answer if you work with older systems.—SA
24 Feb 2012 by Chandrakantt
9 Apr 2012 by nv3
Difficult to answer without knowing what level of access your users have. If a user has administrator right there is in my opinion no way of totally hiding a file from him. That would be counter-productive, because as an administrator I am expected to have access to all files on the...
26 Sep 2014 by Abani Kumar Meher
This article explains few scenarios where XSS attack can be done, how we make mistake while creating web application which leads to XSS vulnerability and what should be done to prevent XSS attacks.
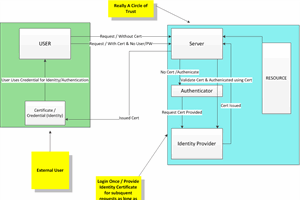
8 Nov 2014 by CdnSecurityEngineer
13 Apr 2015 by Richard Deeming
You're passing different strings to the method.In a C# string literal, "\n" represents a new-line character (ASCII code 10).In a VB string literal, "\n" represents a back-slash (ASCII code 92) followed by a lower-case "n" (ASCII code 110).Either change your C# code to use a verbatim...
24 Dec 2015 by Gaurav Aroraa
8 Nov 2018 by DataBytzAI
Overview of encryption at rest, in motion and in use with Azure Encryption
19 May 2021 by Ohad Redlich
authentication-flows-js is a powerful and highly customizable middleware for Node.js that covers all flows that any express-based authentication-server needs
26 Sep 2021 by Jason Sultana
18 Oct 2021 by Matthew Casperson
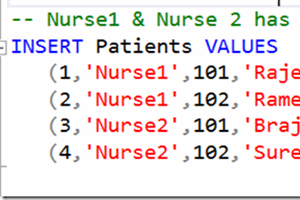
11 Jul 2023 by Andre Oosthuizen
11 May 2010 by Dalek Dave
Is there a way of disabling the USB ports?(Yes, I know, open box, cut wires!)I meant either through the OS or programmatically.I am required to put a machine in an unsecured location, and want to protect it from nasty little people with grubby protruberances from sticking anything on...
11 May 2010 by dan!sh
15 May 2010 by #realJSOP
You can't prevent someone from copying the CD, but you can prevent them from using anything ON the CD via enryption that can only be accessed with a hardware USB dongle installed on the machine.In short, you're going to make it such a huge pain in the ass for your users that they will...
28 Dec 2010 by Aman4.net
Dear cyberm0t0,I would like to tell that while you are using database in your project you need to write ConnectionString in your code to establish connection. No other settings are required.Best place to write ConnectionString is Web.config (in Web Project) and App.config (in window...
3 Jan 2011 by #realJSOP
You have to write a Windows service and install it on all of the affected systems. The Windows service would check a database (on a separate database server) that contains the association data (which USB key is associated with which user and/or machine).BTW, how are you planning on...
19 Jan 2011 by Nish Nishant
See http://msdn.microsoft.com/en-us/library/aa375685(VS.85).aspx[^]Based on that 0x80880283 is CAPICOM_E_ENVELOP_RECIPIENT_NOT_FOUND. More details:The recipient cannot be found in the EnvelopedData object. Usually, this does not happen with an EnvelopedData object that was created...
1 Feb 2011 by #realJSOP
I have an app that can mostly run as the current non-admin user, but some features of the app (user-activated by way of a button click) need to have admin privileges to work. I want the UAC to pop up when the user tries to use these privileged features, but I don't want to have to run the app...
6 Feb 2011 by Nish Nishant
There's no foolproof and universal way to do this. What people typically do is to encrypt the data (and not the disk).[Update - in response to your comment]You could write a custom usb driver and then have a non-standard usb stick manufactured. It would still connect via USB but without...
24 Mar 2011 by Eduard Keilholz
Hey!There are a couple of solutions available to accomplish that. If you want a real secure solution, you'll need to have USB-Dongles with a public & private key pair. You may for example use this[^] hasp.If you don't want a real secure solution you can develop something yourself (for...
24 Mar 2011 by #realJSOP
Personally, I would never use a piece of software that required a dongle be plugged in so that it would run. You'd be better off having it verify itself over the internet, which could be easily configured to allow the software to run a certain number of times without an internet connection...
7 Aug 2011 by Dalek Dave
21 Aug 2011 by Dalek Dave
24 Aug 2011 by André Kraak
I found this[^] on stackoverflow:You could setup folder security to prevent the user's from accessing/deleting from the drive.Give the application a set of credentials it can use to access/manipulate the drive.You could either setup the system to run as a specified user (eg "run as" or...
24 Feb 2012 by Pranit Kothari
Hi All,I wanted to create a web filter either in C# or C++. I have search about this on Google, but didn't any relevant information. Exactly what I want is if someone tried to open "xyz.com", it should be redirect to localhost.. please do not suggest hosts file, it is very simple to...
10 May 2012 by Richard MacCutchan
This question is not appropriate for this forum, which offers technical Question and Answer support. It is unlikely that anyone will have the time or inclination to read this paper on your behalf and explain its content to you.This is only urgent to you, most people here already have their...
19 Jul 2012 by StianSandberg
This is because you don't have permission to do SELECT's on that table. Ask your dba to give you permission.Grant permission sql-script:GRANT INSERT, UPDATE, SELECT ON YourTable TO User1, User2Giving and removing permissions in SQL Server[^]
27 Nov 2012 by Paulo Buchsbaum
1 Jan 2013 by Karl Stoney
In this post, I will show you how to handle automatic encryption and decryption of hidden form fields using Rijndael.
6 Feb 2013 by Richard MacCutchan
I think you actually mean binary comparisons, rather than hex. However, just scanning a file and comparing it with a known virus pattern will not guarantee that the file is also a virus. There are many other checks that need to be done, including checking for embedded code changes that may turn...
7 Feb 2013 by Sergey Alexandrovich Kryukov
7 Mar 2013 by Michael Haephrati
18 Mar 2013 by Rohit Kumar Mumbai
To completely bypass this warning and still run programs as an administrator, do the following:-1) Start, Run, secpol.msc2) Click on Local Policies, Security Options3) Scroll down to this setting: "User Account Control: Behavior of the elevation prompt for administrators in Admin...
30 Apr 2013 by Balimusi
WCF might be a good option for you. You can take advantage of the attributes that WS-Security provides – it describes how to handle security issues within the SOAP messages. WS-Security assigns the signature and encryption information as well as the security tokens to the SOAP messages. Besides...
17 Feb 2014 by Sergey Alexandrovich Kryukov
25 Feb 2014 by Sergey Alexandrovich Kryukov
Please see my past answer, it shows most tricky part of it, manipulation with the header/metadata: Writting Header wav in wav.file[^].(You can automatically translate C# to VB.NET, but it's enough to understand the idea; I referenced the document I used.)See...
2 Aug 2014 by CdnSecurityEngineer
15 Feb 2015 by Kornfeld Eliyahu Peter
If HTTPS used that means that under (before) the HTTP transfer there is a secure layer (SSL or TLS). These methods are using a public/private key pair to make the encryption possible. The method ensures that no-one sitting on the lines can read the transferred data... (HTTPS[^]).If you are...
26 Jun 2015 by Member 11794279
16 Sep 2015 by F-ES Sitecore
You can't create files that can't be deleted or else viruses would be impossible to get rid of. If the user wants to delete those files then your app stops working (or you can re-create fresh copies), that's their decision.
6 Mar 2016 by OriginalGriff
"This a homework And the teacher asked for this"And that means he wants your thoughts: not ours.We do not do your homework: it is set for a reason. It is there so that you think about what you have been told, and try to understand it. It is also there so that your tutor can identify...
17 Jul 2016 by Andy Point
Firebase Android Tutorial : Adding Registration and Login Hello Developers, this is our android firebase tutorial. In this tutorial we will create an android firebase app that will use firebase android login functionality. This post will help you get you up and running with integrating Firebase to a
18 Jul 2016 by Patrice T
30 Aug 2016 by Taiseer Joudeh
This is the third part of the tutorial which will cover Using Azure AD B2C tenant with ASP.NET Web API 2 and various front-end clients. Azure Active Directory B2C Overview and Policies Management – (Part 1) Secure ASP.NET Web API 2 using Azure AD B2C – (Part 2) Integrate Azure Active Dir
19 Sep 2016 by Mehdi Gholam
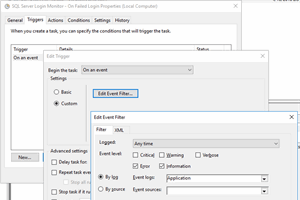
30 Apr 2018 by Ryan G Conrad
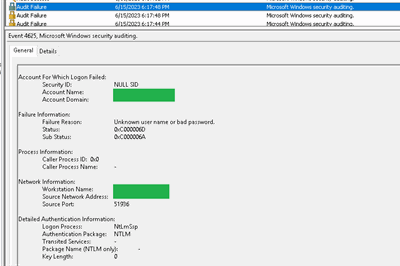
Using Powershell and Windows Task Scheduler API to detect malicious login attempts on a remotely accessible SQL Server database
5 Jul 2020 by Patrice T
10 Jan 2022 by Afzaal Ahmad Zeeshan
Introduction and Background As the title suggests, this post is a personal recommendation for the users of Microsoft Cognitive Services, the services that provide a cloud-based subscription-based solution for artificially intelligent software applications, with an any team, any purpose and any scale
4 May 2023 by Bruno van Dooren
12 Feb 2023 by Divya Ulasala
13 Jun 2023 by Peng Qiu
21 Jun 2023 by Bruno van Dooren
2 Jan 2024 by Viktoria Dolzhenko
11 Jun 2020 by Imran Abdul Ghani
29 Jan 2010 by Wags
24 Feb 2010 by Alaric Dailey
24 Feb 2010 by Andreas Mertens
Has anyone used the System.Security.AccessControl.CustomACE class to create a custom ACE? How do I go about doing this?I am writing a BHO (Browser Helper Object) which in IE7/8 runs with Mandatory Integrity Low permissions. I am also going to launch a "helper object" that will run with...
20 Apr 2010 by Christian Graus
22 Apr 2010 by #realJSOP
11 May 2010 by Pete O'Hanlon
If I were you, I'd look to create a local security policy and put it in place. This policy could limit access to only certain parts of the hard drive, and disable input from any other sources. For things like this, a security policy is a better bet.If you don't want to go that route, you can...