- home
- articles
- quick answersQ&A
-
discussionsforums
- CodeProject.AI Server
- All Message Boards...
- Application Lifecycle>
- Design and Architecture
- Artificial Intelligence
- ASP.NET
- JavaScript
- Internet of Things
- C / C++ / MFC>
- C#
- Free Tools
- Objective-C and Swift
- Database
- Hardware & Devices>
- Hosting and Servers
- Java
- Linux Programming
- Python
- .NET (Core and Framework)
- Android
- iOS
- Mobile
- WPF
- Visual Basic
- Web Development
- Site Bugs / Suggestions
- Spam and Abuse Watch
- featuresfeatures
- communitylounge
- help?
Everything / Security
Security
security
Great Reads
by The Ænema
Inject your 4.
by Michael Haephrati
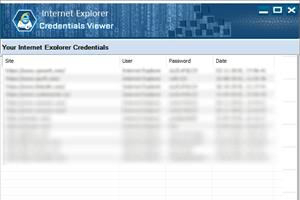
Chrome stores all passwords and other credentials in an encrypted database but guess what: they can be retrieved by anyone with the proper knowledge.
by Ajay K. Yadav
The objective of writing this paper is to manifest,
by Kewin Rausch
An introduction on how these applications self-defend themselves against scanning techniques,
Latest Articles
by Jason Sultana
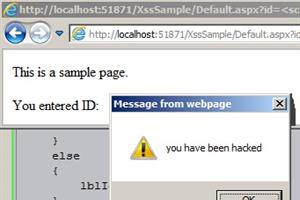
This article discusses Cross Site Scripting (XSS),
by Wessel Beulink
What is Azure Virtual Network Encryption? Azure Virtual Network encryption provides a layer of security that encrypts virtual network traffic,
by Zijian
Reusable codes for JWT security in business applications
by Federico Di Marco
A tool which creates one or more Powershell scripts which in turn recreate one or more binary files
All Articles
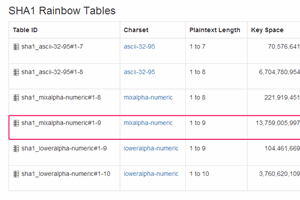
28 Oct 2014 by Ajay K. Yadav
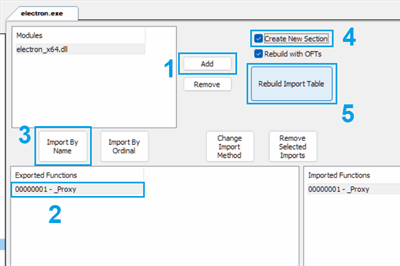
The objective of writing this paper is to manifest, how to crack an executable without peeping its source code by exercising OllyDbg tool.
30 Jan 2017 by Michael Haephrati
20 Jun 2013 by Levente Kupás
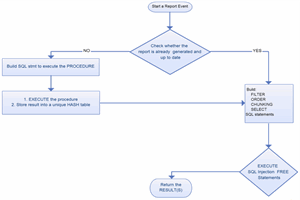
If you have big reports which run slowly, you may use this T-SQL based engine to speed-up them.
10 Mar 2018 by Joe Dillon
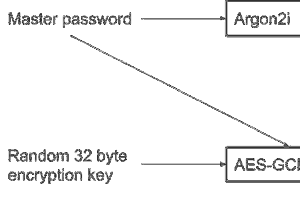
This article describes the security techniques required to create a secure offline password manager and how the Libsodium library has been used to achieve this. YAPM stores passwords with AES encryption and authenticates users with an Argon2 hash.
16 Jan 2023 by The Ænema
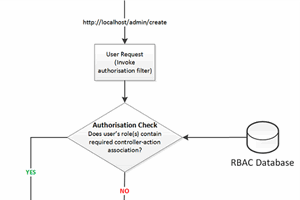
10 Nov 2018 by DataBytzAI
18 Feb 2019 by Apriorit Inc, ruksovdev
A detailed description of an FPGA-specific framework called ISE Design Suite, and the main steps you need to take in order to create a VGA driver using FPGA
26 Sep 2014 by Abani Kumar Meher
This article explains few scenarios where XSS attack can be done, how we make mistake while creating web application which leads to XSS vulnerability and what should be done to prevent XSS attacks.
8 Nov 2018 by DataBytzAI
Overview of encryption at rest, in motion and in use with Azure Encryption
19 May 2021 by Ohad Redlich
authentication-flows-js is a powerful and highly customizable middleware for Node.js that covers all flows that any express-based authentication-server needs
18 Oct 2021 by Matthew Casperson
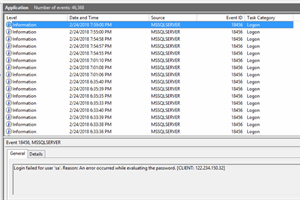
30 Apr 2018 by Ryan G Conrad
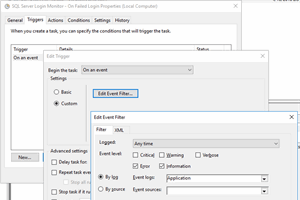
Using Powershell and Windows Task Scheduler API to detect malicious login attempts on a remotely accessible SQL Server database
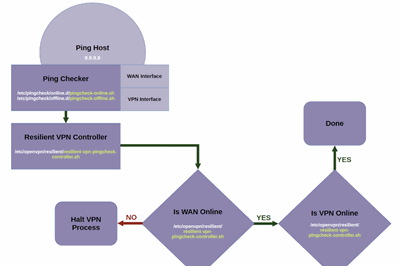
4 May 2023 by Bruno van Dooren
13 Jun 2023 by Peng Qiu
2 Jan 2024 by Viktoria Dolzhenko
11 Jun 2020 by Imran Abdul Ghani
11 Oct 2013 by ASP.NET Community
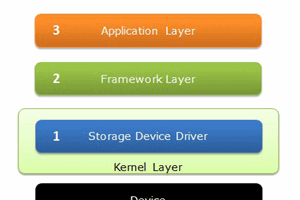
30 Oct 2015 by Android on Intel
22 May 2016 by RajeshKumar D
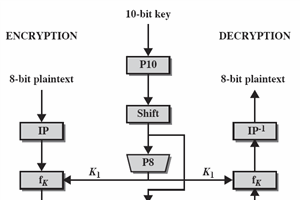
Configuring PGP Encryption and Decryption part of MULE ESB
18 Jan 2017 by Alibaba Cloud
Here are five top tips from our expert team to help you maximize the benefits of your cloud infrastructure.
30 Aug 2018 by Member 10280272
The focus in this article is on avoiding over-the-wire security issues that can be addressed in web pages.
24 Jan 2019 by Apriorit Inc, MikeSotnichek
5 Feb 2019 by Apriorit Inc, MikeSotnichek
The experience of creating a custom blockchain network using the Graphene framework.
8 Jan 2022 by Michael Sydney Balloni
12 Oct 2023 by Viktoria Dolzhenko
An introduction to the concept of DAO and a workshop on how to create your own
13 Nov 2023 by Chris Maunder
In this article we will explore how self-hosted AI, specifically CodeProject.AI Server, empowers businesses to leverage the power of AI while maintaining control over their data.
1 Mar 2011 by Bryian Tan
20 Sep 2012 by Russel Beutler
Whether you’re developing for unmanaged small business, or enterprise-level IT departments, 3rd Generation Intel® Core™ processor-based PC and mobile platforms are designed to help you meet the needs of your customers.
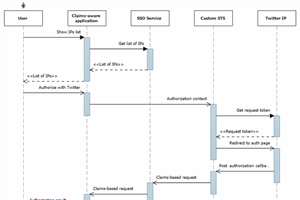
11 Oct 2013 by ASP.NET Community
11 Oct 2013 by ASP.NET Community
11 Oct 2013 by ASP.NET Community
It's absolutely necessary if you're serious about security.Whitepapers/Books/BlogsThreat Modeling for ASP.NET (PDF) - an excellent white
11 Oct 2013 by ASP.NET Community
11 Oct 2013 by ASP.NET Community
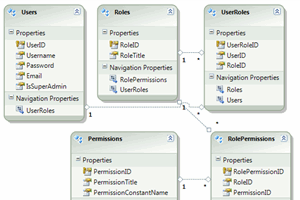
Here are a few good tutorial articles that provide a good conceptual overview of how the new membership and role management system works. Check out
11 Oct 2013 by ASP.NET Community
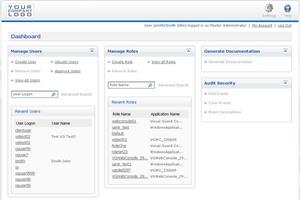
11 Jul 2014 by Jeffrey T. Fritz
I’ve been reviewing Novalys Visual Guard for the last 2 weeks, and found some really interesting nuggets in this package that would make my network administrators stand up and take notice.
29 Sep 2014 by Dirk_Strauss
Acunetix WVS audits your website security by running a host of tests. It then provides a concise report of issues it found. Not only does it do this, but it also suggests changes you need to make to fix the issues found.
17 Nov 2014 by Android on Intel
1 Dec 2015 by Mark_Warren
Working with customers and partners, here is an overview of the need for DevSec and the five ‘best practice’ questions to ask when looking how to have a better ‘DevSec’ strategy
14 Jan 2016 by Android on Intel
Intel® Hardware-based Security Technologies Bring Differentiation to Biometrics Recognition Applications
14 Jan 2016 by Android on Intel
I will describe a new way to implement security for sensitive data based on eCryptfs (eCryptfs.org).
1 Feb 2016 by Android on Intel
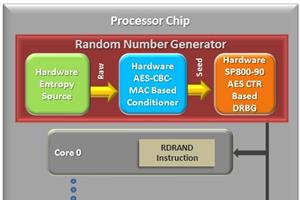
High Performance and Security Software-Based Encryption by Intel® Advanced Encryption Standard New Instructions and Intel® Secure Key
26 Sep 2016 by Yuri Diogenes
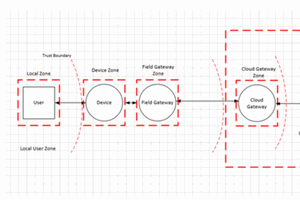
The objective of threat modeling is to understand how an attacker might be able to compromise a system and then make sure appropriate mitigations are in place. Threat modeling forces the design team to consider mitigations as the system is designed rather than after a system is deployed.
19 Jan 2017 by Rich Dost
In this first episode we'll tackle the first thing, security. We are at the start of a journey. We'll learn about many Predix services and components. We'll find the good, the bad and the ugly, and we'll complain the whole way. After security we'll hit Asset and Analytics.
24 Feb 2017 by Intel
9 Jan 2019 by Apriorit Inc
Two theoretical ways to protect a Linux kernel module from hooks.
17 Jan 2019 by Apriorit Inc
22 Jan 2019 by Apriorit Inc, Sergey Stepanchuk
15 Mar 2019 by Apriorit Inc, MikeSotnichek
16 Jul 2023 by hemanthk119
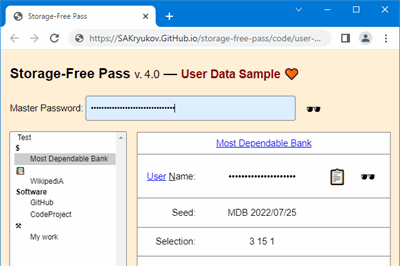
28 Dec 2022 by Sergey Alexandrovich Kryukov
Generator of highly secure passwords based on cryptographic hash and master password, which should be memorized; no password storage is involved.
25 Mar 2018 by Ryan G Conrad
13 Jan 2020 by Dominik Reichl
15 Apr 2015 by webmaster442
13 Nov 2021 by The Ænema
11 Jun 2012 by taha bahraminezhad Jooneghani
14 Feb 2016 by adriancs, Taylor Hornby
15 May 2023 by Bruno van Dooren
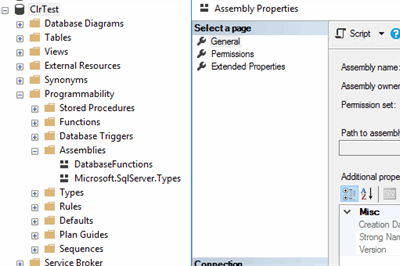
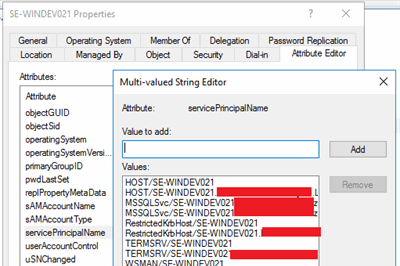
Basics of Service Principal names, and what they mean for SQL Server security
16 Jul 2018 by Paul D. Sheriff
17 May 2018 by Sriganesha Rao
This article provides an overview of ASP.NET Core security features.
6 Apr 2013 by Rahul Rajat Singh
20 Jul 2012 by StianSandberg
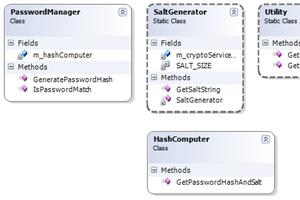
This article will explain how to securely store users passwords in a database.
26 Sep 2012 by Vitaly Zhukov
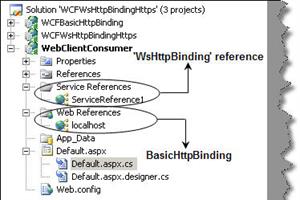
25 Jul 2010 by Fayaz Soomro
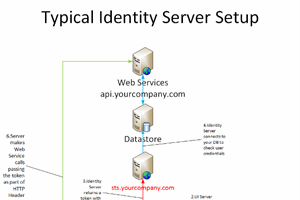
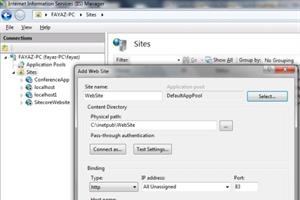
This article describes custom username password authentication without the need of certificate installation on the client side.
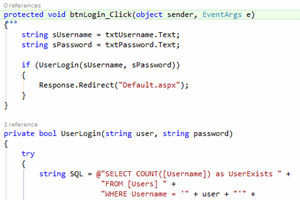
4 Aug 2016 by Saineshwar Bageri
11 Oct 2011 by Scott Clayton
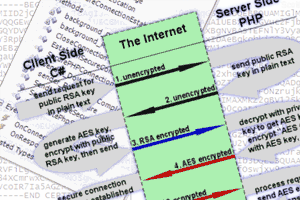
Set up encrypted secure communication between C# and PHP using the AES and RSA algorithms.
16 Jul 2014 by Himanshu Thawait
15 Mar 2012 by Mohammad Sepahvand
19 Mar 2013 by Anupama Agarwal
16 Jul 2014 by Rahul Rajat Singh
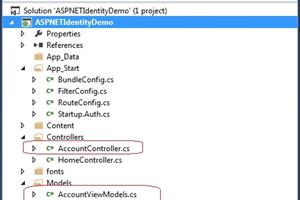
In this article we will look into ASP.NET Identity System which comes as the default authentication and authorization mechanism with ASP.NET MVC 5 internet application template. We will try to understand the ASP.NET Identity system and compare it with the ASP.NET simple membership providor and the c
9 Jan 2013 by Rahul Rajat Singh
21 Apr 2011 by All Time Programming
Verifying the Server Certificate on the client side using a CA file
27 Jan 2014 by GustavoMartins
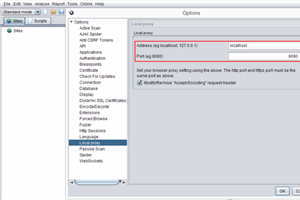
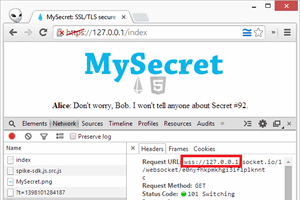
Automate your penetration testing using the pentest tool ZAP and the
21 Mar 2016 by Dharmesh_Kemkar
18 Jun 2012 by Shivprasad koirala
16 Jul 2018 by Paul D. Sheriff
A technique for securing Angular 2/6 applications
3 Jul 2019 by rtybase
2 Mar 2024 by Federico Di Marco
A tool which creates one or more Powershell scripts which in turn recreate one or more binary files